June 25, 2021
Learn how to bring together your NLDM and CCS models to reach timing closure faster with Solido Analytics.
June 21, 2021
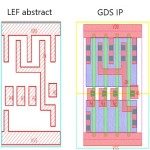
Overcome problems created by mismatches between library exchange format (LEF) and GDS or OASIS representations to avoid design delays.
May 31, 2021
Using on-demand rule checks during place-and-route boosts efficiency and design quality.
May 3, 2021
Learn how power-intent, LDEs, ESD and voltage-aware spacing techniques can particularly benefit from the use of static verification checks.
April 9, 2021
The best paper winner at DVCon 2021 details a comprehensive methodology for making the best use of formal verification for bug hunting
April 6, 2021
Joe Sawicki of Siemens EDA recently addressed the main trends in design delivery from architecture to validation to digital twins - and where they may soon take the industry and its products.
March 1, 2021
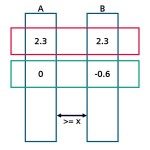
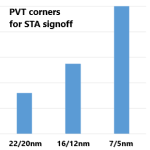
From 16nm, new complexities hinder .lib file characterization and verification but machine learning now offers an efficient way of managing them.
December 10, 2020
With features that keep it in current use such as aspect-oriented programming, the e language can leverage integrated design environments. Learn how.
December 9, 2020
Invocation GUIs play an important role in delivering efficient verification runs. Learn how to take advantage of the features within Calibre Interactive.
October 26, 2020
One roadblock to the integration of IP from multiple vendors into an SoC is the likelihood of finding duplicate cell names in the merged design. Carefully considered renaming strategies can fix the problem without causing design database bloat.