January 13, 2022
More optimistic about the semiconductor industries prospects than for some time, Siemens Joe Sawicki identified key EDA challenges at DAC.
April 6, 2021
Joe Sawicki of Siemens EDA recently addressed the main trends in design delivery from architecture to validation to digital twins - and where they may soon take the industry and its products.
January 28, 2019
The second part of this feature looks at how Wave Computing's objectives with its dataflow processing unit for AI mapped to the use of emulation in its development.
January 25, 2018
Building secure SoCs takes a methodical approach, careful study of possible attacks, and embedded hardware that can provide a Root of Trust
January 11, 2017
A look at the steps necessary to validate implementations of the cryptographic algorithms that are used to protect today’s devices and communications infrastructure.
October 21, 2015
Part three of our series looks at the choices you face as you decide whether to build or buy a board.
September 28, 2015
Part two of our series on FPGA-based prototyping looks at two critical factors to address before a project begins: budgeting and high-level implementation.
September 7, 2015
This multi-part series addresses various aspects of FPGA-based prototyping. Future installments will address budgeting and implementation, but we start by looking at why the technique is generating so much interest.
August 19, 2014
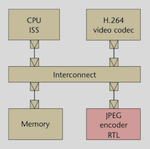
This article introduces hybrid emulation, a combination of emulation and virtual prototypes, and its application to tasks such as architecture validation, early software development and software-driven verification.
March 7, 2012
An evolved ESL-to-RTL methodology flow addresses the ‘discipline gaps’ between software and hardware engineering by using three system level-based software-hardware verification steps. The strategy is already available in TSMC’s Reference Flow 12.