IP Topics
-
Debugging complex RISC-V processors
RISC-V adoption is growing fast as is the ecosystem around the open-source core. Hardware and software are now vital for appropriate debug.
-
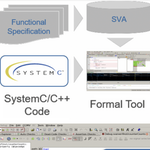
Formal verification for SystemC/C++ designs
Automated formal technologies can be used to ease the debug and functional verification burden of SystemC/C++ code prior to high-level synthesis. This tutorial, first presented at DVCon Europe explores how these formal techniques can be deployed and provides real-world examples.
-
How to use runtime monitoring for automotive functional safety
The promise of autonomous vehicles is driving profound changes in the design and testing of automotive ICs.
-
Introduction to the Compute Express Link (CXL) protocols
A look at the key protocols that control the Compute Express Link (CXL) standard for connecting CPUs and accelerators in hetereogenous computing environments.
Assembly & Integration
Design Management
- Expert Insight Improved power management and faster time to market?
- Expert Insight How to migrate SoC design to the cloud
- Expert Insight Give the people what they want: toward making 3D IC mainstream
Selection
PLATINUM SPONSORS



View All Sponsors