December 14, 2018
Antifuse-based OTP NVM is highly scalable, has the area efficiency to enable macros of megabit capacities, and offers low read power.
November 5, 2018
The basics of USB 3.2, how to implement it in an SoC, and how USB Type-C connectors and cables are used in USB 3.2 systems.
October 16, 2018
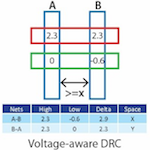
How you can use the dedicated rule decks now being provided by foundries as the foundation for a reliability verification flow.
October 16, 2018
As AI becomes pervasive in computing applications, so too does the need for high-grade security in all levels of the system.
October 9, 2018
The proliferation of attacks against embedded systems is making designers realize that they need to do more to secure their products and ecosystems.
September 23, 2018
Machine-learning strategies for embedded vision are evolving so quickly that designers need access to flexible, heterogenous processor architectures that can adapt as the algorithms evolve.
August 13, 2018
Dina Medhat describes what you need to know about the types of waiver strategy that can be applied.
August 2, 2018
Designers need to understand how the architecture of electronic control units used to implement ADAS in vehicles is changing.
July 11, 2018
Choosing the right crypto processor implementation involves a complex set of design tradeoffs between speed, area, power consumption and flexibility. Using consistent benchmarks can help explore your options.
June 20, 2018
An evolution of the Ethernet standard enable time-sensitive networking with the predictable latencies and guaranteed bandwidth necessary for automotive applications.