March 8, 2022
The Covid-driven MCU shortage for ECUs and elsewhere in vehicle design can bring entire production lines to a halt if not properly managed.
March 3, 2022
Because of the high analog content in memory designs, designers must understand how various effects impact reliability and performance.
January 27, 2022
Generating accurate ASIL metrics early in the functional safety lifecycle, reduces time-to-certification for ISO26262.
January 13, 2022
More optimistic about the semiconductor industries prospects than for some time, Siemens Joe Sawicki identified key EDA challenges at DAC.
January 12, 2022
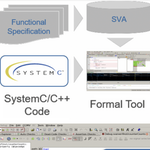
Automated formal technologies can be used to ease the debug and functional verification burden of SystemC/C++ code prior to high-level synthesis. This tutorial, first presented at DVCon Europe explores how these formal techniques can be deployed and provides real-world examples.
December 15, 2021
Learn how Calibre 3D enables circuit and layout verification multi-die assemblies so that heterogeneous die processes can co-exist without significant impact to the deck.
November 12, 2021
Pre- and post-processing EDA techniques help streamline design rule checks and delivery efficient waivers to speed design and debug.
November 4, 2021
PIM memory boosts efficiency by operating on data without moving it to the CPU but realizing this type of novel technology posed power integration and planning challenges.
October 21, 2021
Innovation is extending the technique's power across areas such as context-aware layout, accounting for multi-patterning and implementing fill.
September 3, 2021
SiP promises advances in transmission speeds, bandwidth, accuracy and low power but verification requires careful evolution of existing tools.